Client Work
Custom-made toolsManaging WordPress Security
Cloudflare WAF defense system and custom-built security tooling for live WordPress sites. Paid client work under the mentorship of IO01.
5-Rule Defense System
Progressive rules that escalate from permissive to restrictive, ensuring legitimate traffic passes while blocking threats. Click any rule to inspect its Cloudflare expression.
-
Skip Allow Good Bots — whitelist the origin server, verified search crawlers, monitoring services, and Let's Encrypt cert renewals
(ip.src in {<SERVER_IP>}) or (cf.verified_bot_category in { "Search Engine Crawler" "Search Engine Optimization" "Monitoring & Analytics" "Advertising & Marketing" "Page Preview" "Academic Research" "Security" "Accessibility" "Webhooks" "Feed Fetcher" }) or (http.user_agent contains "letsencrypt" and http.request.uri.path contains "acme-challenge") -
Challenge Aggressive Crawlers — challenge known SEO tools, scrapers, and unverified bots by user-agent patterns
(http.user_agent contains "yandex") or (http.user_agent contains "sogou") or (http.user_agent contains "semrush") or (http.user_agent contains "ahrefs") or (http.user_agent contains "baidu") or (http.user_agent contains "python-requests") or (http.user_agent contains "neevabot") or (http.user_agent contains "CF-UC") or (http.user_agent contains "sitelock") or (http.user_agent contains "crawl" and not cf.client.bot) or (http.user_agent contains "bot" and not cf.client.bot) or (http.user_agent contains "Bot" and not cf.client.bot) or (http.user_agent contains "Crawl" and not cf.client.bot) or (http.user_agent contains "spider" and not cf.client.bot) or (http.user_agent contains "mj12bot") or (http.user_agent contains "ZoominfoBot") or (http.user_agent contains "mojeek") or (ip.src.asnum in {135061 23724 4808} and http.user_agent contains "siteaudit") -
Challenge Challenge Large Providers / Country — challenge cloud provider ASNs (AWS, Azure, GCP) and traffic from outside the allowed country list
(ip.src.asnum in {7224 16509 14618 8075 396982} and not cf.client.bot and not cf.verified_bot_category in { "Search Engine Crawler" "Search Engine Optimization" "Monitoring & Analytics" "Advertising & Marketing" "Page Preview" "Academic Research" "Security" "Accessibility" "Webhooks" "Feed Fetcher" "Aggregator" }) or (not ip.src.country in {"IL" "SA" "AE" "EG" "JO" "LB" "MA" "IT" "US" "GB"} and not cf.client.bot and not cf.verified_bot_category in { "Search Engine Crawler" "Search Engine Optimization" "Monitoring & Analytics" "Advertising & Marketing" "Page Preview" "Academic Research" "Security" "Accessibility" "Webhooks" "Feed Fetcher" "Aggregator" } and not http.request.uri.path contains "acme-challenge" and not http.request.uri.query contains "?fbclid" and not ip.src.asnum in {32934}) -
Challenge VPN / Path Managed Challenge — challenge known VPN provider ASNs and any access to the WordPress login path
(ip.src.asnum in { 60068 9009 16247 51332 212238 131199 22298 29761 62639 206150 210277 46562 8100 3214 206092 206074 206164 213074 }) or (http.request.uri.path contains "wp-login") -
Block Block Web Hosts / Paths / TOR — hard block web hosting ASNs, sensitive WordPress paths, TOR exit nodes, and AI crawlers
(ip.src.asnum in { 200373 198571 26496 31815 18450 398101 50673 7393 14061 205544 199610 21501 16125 51540 264649 39020 30083 35540 55293 36943 32244 6724 63949 7203 201924 30633208046 36352 25264 32475 23033 32475212047 32475 31898 210920211252 16276 23470 136907 12876 210558132203 61317 212238 37963 13238 2639 20473 63018 395954 19437207990 27411 53667 27176 396507206575 20454 51167 60781 62240398493206092 63023 213230 26347 20738 45102 24940 57523 8100 8560 6939 14178 46606 197540397630 9009 11878 }) or (http.request.uri.path contains "xmlrpc") or (http.request.uri.path contains "wp-config") or (http.request.uri.path contains "wlwmanifest") or (cf.verified_bot_category in {"AI Crawler" "Other"}) or (ip.src.country in {"T1"})
Strategy
A conservative, data-driven approach that minimizes disruption to legitimate users.
Custom Tools
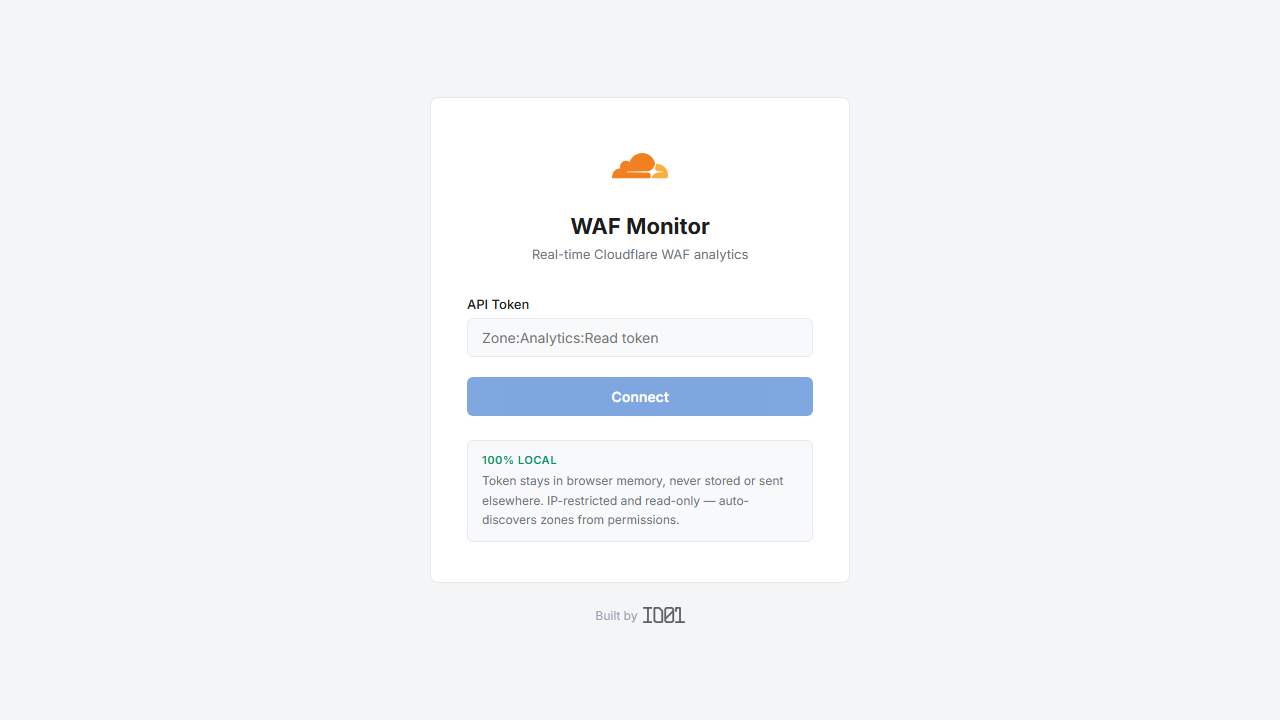
Cloudflare's free plan doesn't include WAF analytics — you can configure rules but fly blind on what they're actually doing. I built WAF Monitor to fill that gap: a custom React dashboard that surfaces real intelligence from the Cloudflare API.
- Real-time threat visibility — blocked IPs, challenge rates, and attack patterns per rule
- Rule effectiveness metrics — which rules trigger most, confirming they work
- Automated threat intelligence — classifies sources, flags anomalies, identifies scanners
- Export reports — single-zone or combined 4-zone HTML/PDF for the client
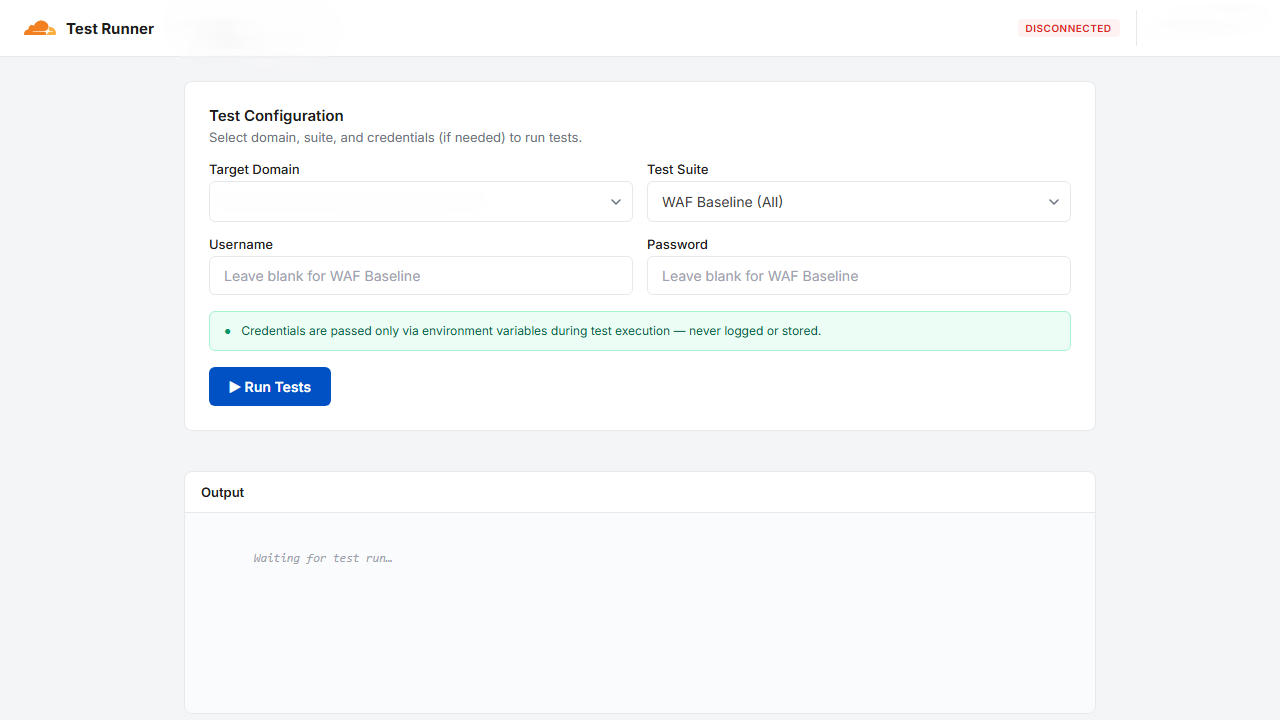
A bespoke Playwright test suite and browser dashboard that validates every WAF rule after each configuration change — ensuring no legitimate user flow is ever interrupted.
- 24 baseline tests — core site, admin, REST API, plugins, static assets
- 31 legitimate-user flow tests — full login flow, enrolled courses, video & slides
- False positive detection — flags any rule that blocks legitimate user access
- Multi-domain support — runs against both production & dev environments